One of the most common errors related to the internet connection in Windows is the “DNS server is not responding”, resulting in loss of access to the Internet. The connection icon will most likely have a yellow triangle, and in the browser, when you try to open the site, you will most likely see the error “Can not find DNS address”, “error name not resolved”, or something similar. In this article, we will try to explain the possible reasons behind this issue and some feasible solution that can be enforced to resolve this problem.
What is a DNS Server?
In the world of computer networking, every system is designated by a specified series of numbers called “IP Address”. These addresses are quite long and difficult to memorize for each system. Hence, in order to simplify the overall communication between systems and operator, networking engineers developed “DNS” (Domain Name System). The function of a DNS is to resolve domain names to numbers. To be specific, it resolves domain names into IP addresses. A DNS system basically works like a phonebook where the IP addresses of thousands of domains are stored alongside their unique IP addresses so that when a user enters a domain name, the DNS server will look for the domain name in the stored database and will automatically redirect you to the corresponding website via the IP address.
check this article to know about DNS Benchmarking Tools for Windows 10.
What is DNS Server Not Responding
This problem is caused by the failure of the DNS server, which is responsible for the redirected IP addresses to the domain. If we talk about the causes of this error, the culprit can be either the computer itself or the router, or the equipment on the provider side. Most of the time, the problem is caused by some misconfiguration on the ISP’s (Internet Service Provider) side. In such cases, there’s not much a user can do to resolve this problem rather than waiting for the ISP service to repair the issue on their own. But, in many cases, it has been observed that this problem may arise due to the presence of meager aberration on the user’s side. in such an event, there are are some proven solutions which can be applied to resolve the problem.
Fix DNS_PROBE_FINISHED_NXDOMAIN Google Chrome error.
How to Resolve DNS Server isn’t Responding
There are following methods which you can practice to fix “DNS Server isn’t Responding” problem. All you will require is a little bit of patience and time. Follow the methods provided below carefully to resolve the problem.
1. Restart your Router/System
Even though this method might sound a little bit novice, we will strongly recommend you to carry out this step before moving forward. As explained above, if the error was caused by your ISP, there are chances that the ISP might already have repaired the problem and all you have to do is reconnect your system with the ISP. Restarting your router/system might help you in this situation because the network configuration settings are verified and recomposed at the time of boot. If the issue gets resolved by a simple reboot, you will definitely save the troubles of going through the lengthy solutions.
2. Check The Status of DNS Client
You must check the status of your DNS client (Service) to verify whether it’s running or not. Sometimes, installation of a third-party software might terminate the DNS client services temporarily for the procedure which will result in the “DNS Server isn’t Responding” problem. To check the status of the service, follow the following steps:
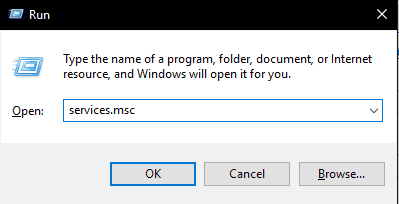
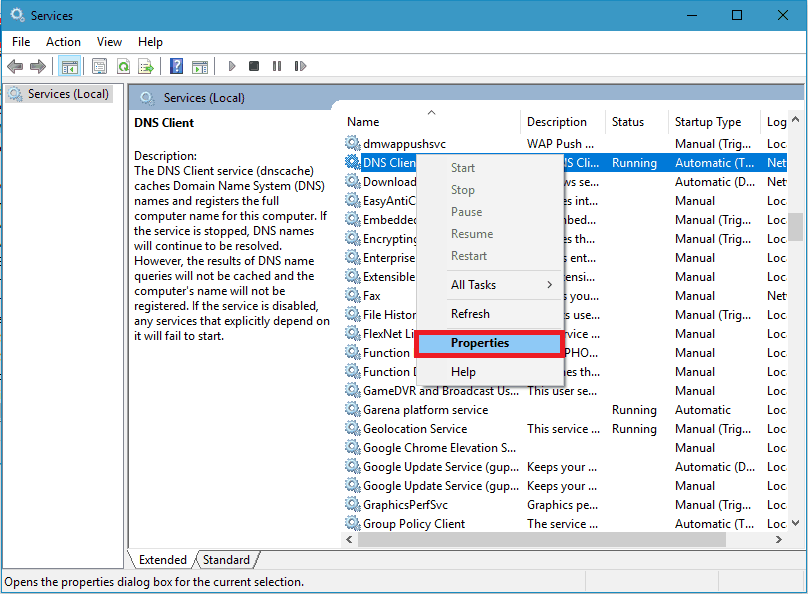
- Press “Windows key + R” to open a “Run Window”.
- Enter “Services.msc” in the space and press “OK”.
- This will open the “Services” window. Here you can see all the services available in your system.
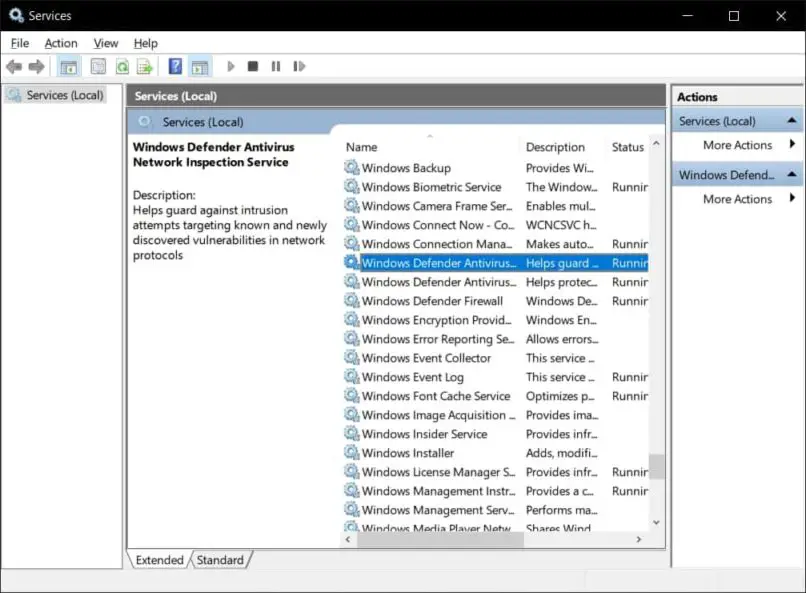
- Look for the “DNS client” service
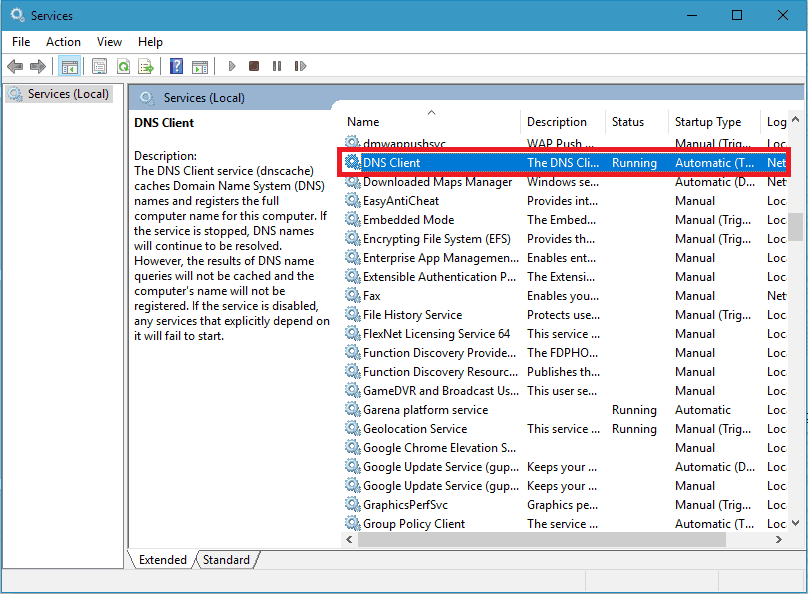
- To check the status of the service, right click on the service and select “Properties”.
- This will open the properties window. Here, Make sure the service status is “Running”. If not, Change the “Startup type” to “Automatic” and click on “Start” button provided just below.
- Reboot the system for changes to take effect.
3. Switch to Google DNS
In case your ISP’s DNS server is not working, you can simply switch to Google’s DNS servers. Google has a free of cost DNS service which you can utilize to resolve the problem. To do so, simply follow the following steps:
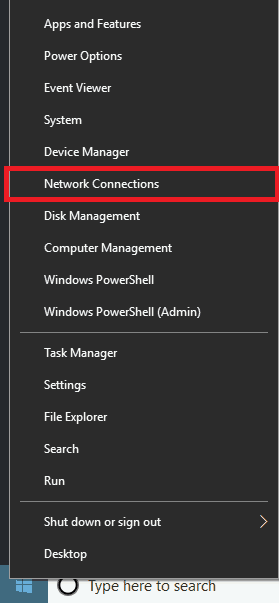
- Right click on the start menu. From the list of options, select “Network Connections”.
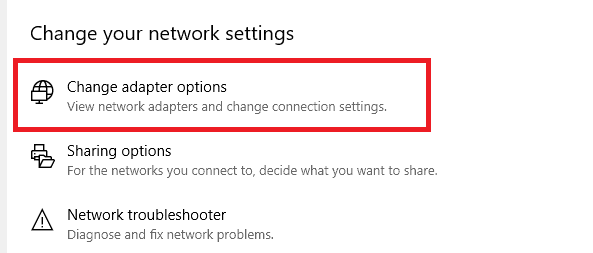
- Now, in the next window, select “Change adapter options”.
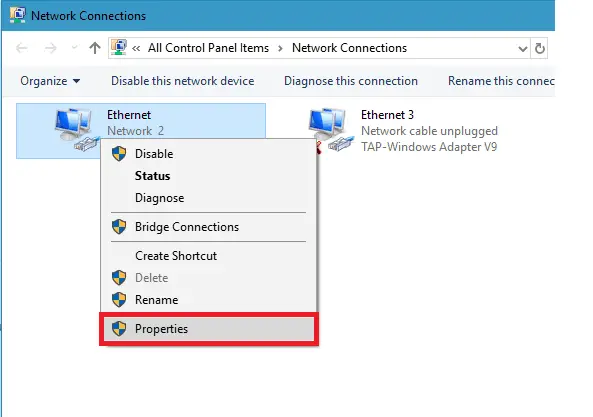
- Locate your current internet adapter in the next window. Right click on the adapter and click on “Properties”.
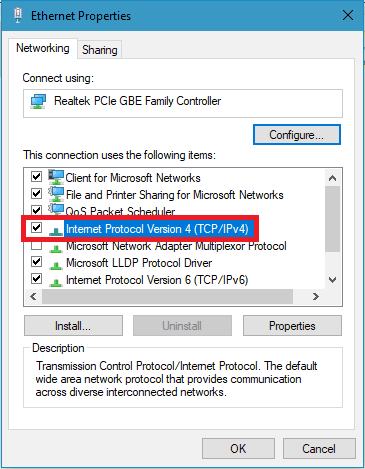
- Now, double click on “Internet Protocol Version 4 (TCP/IPv4)”.
- Now, make sure you check the “Use the following DNS server address” option. After that, Enter ” 8 . 8 . 8 . 8″ in the Primary DNS server and “8 . 8 . 4 . 4” in the secondary DNS server respectively.
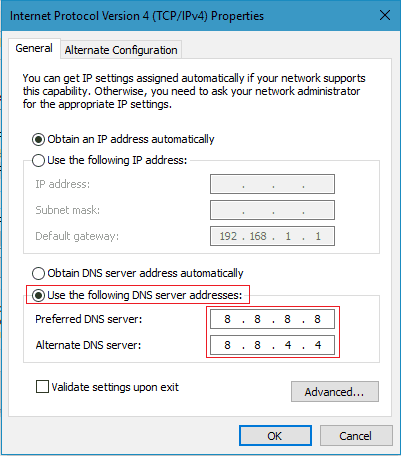
- Once done, Click on “OK” to save the changes. Close the window and restart the system for successful completion.
4: Reset DNS to the Default Value
You can simply utilize the command prompt to clear the DNS cache and reset the network settings. This will definitely remove any error caused due to a misconfiguration in the system’s network properties. To carry out this method, simply follow the steps provided below:
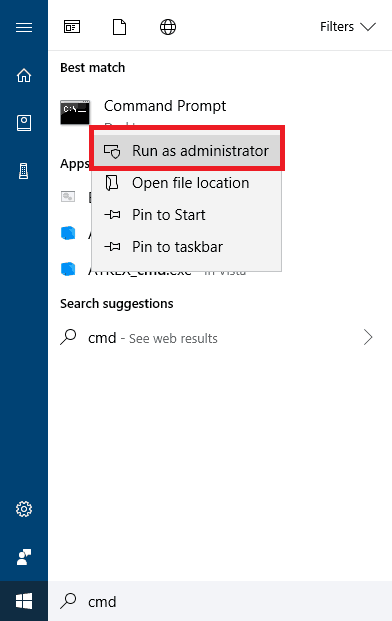
- Press “Windows key” to open the start menu. Type “Cmd” in the search bar and run the command prompt as administrator as shown in the image below.
- In the command prompt, You must execute the following command in the given order.
ipconfig / flushdns ipconfig / registerdns ipconfig / renew ipconfig / release - Simply copy the individual command line and right click in the command prompt to paste it. e.g.,
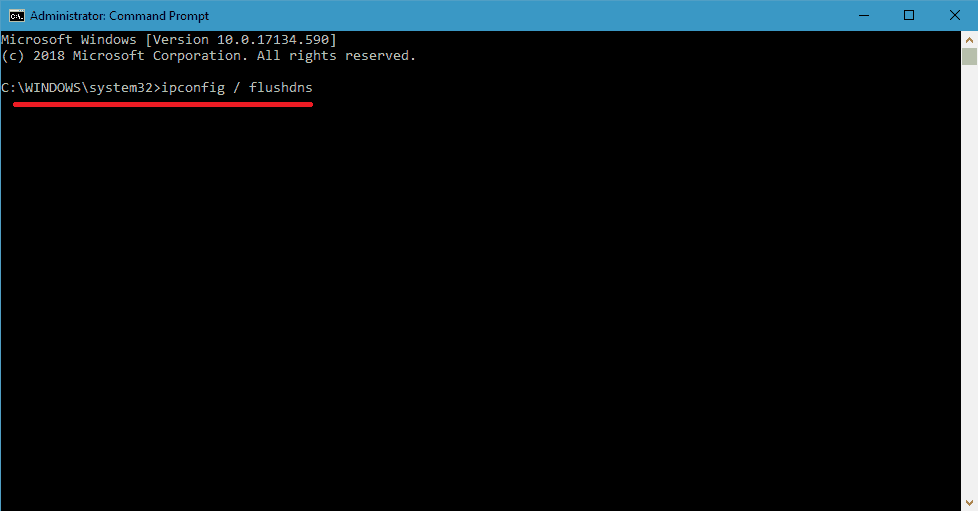
- Now, simply press “Enter” to execute the command. Follow the procedure for all commands.
- Once all the commands have been executed successfully, restart the system for changes to take effect.
5. Update Network Drivers
You can simply update your existing network drivers to resolve the problem. To do so, follow the steps provided below:
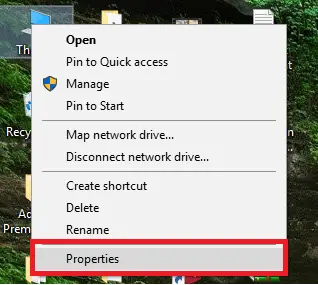
- Right click on “This PC”. Then select “Properties” from the options.
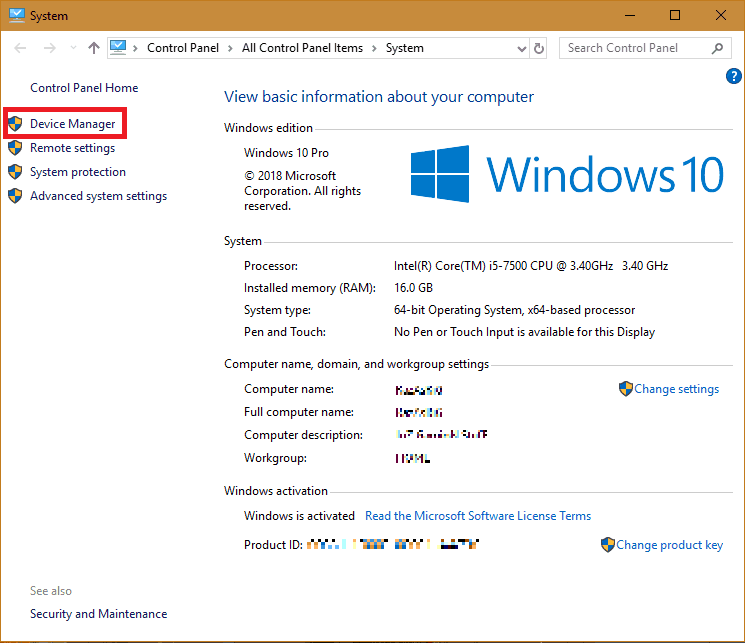
- Select “Device Manager” from the system properties window.
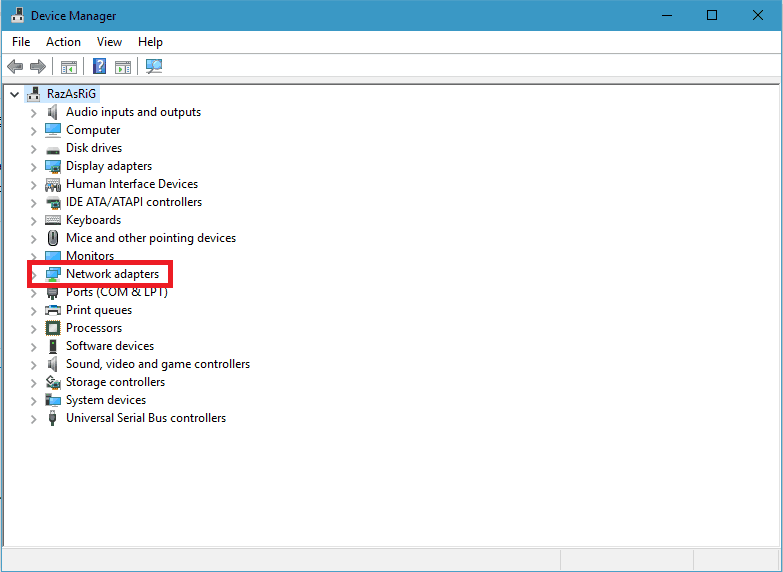
- Now, Open the “Network adapters” menu.
- Here, you’ll see all the available network adapters in your system. To update the adapter, simply right-click on the adapter and select “Update driver”.
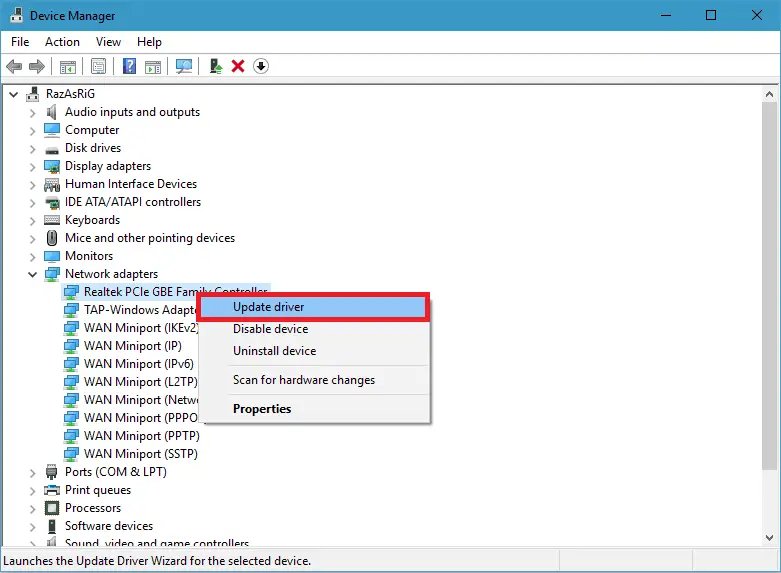
- We will recommend you to update all the available network adapter to avoid any further discomfort.
- Restart the system afterward for changes to take effect.
6. Turn off Firewall
If you are using third party antivirus software which also offers firewall, then you must disable firewall first and check if that’s not the probable cause of DNS server isn’t responding error on Windows 10. The steps to disable firewall varies from software to software and you will have to refer to help documents and guides provided by antivirus and firewall developers. In most cases you can access menu to control firewall and antivirus scanner right from the system tray icon right click context menu.
7. Internet Troubleshooter – Find and Fix Network Problems
Windows 10 comes with plenty of troubleshooting and fixing utilities. One such utility is “Internet Connections” troubleshooter. In order to run it,
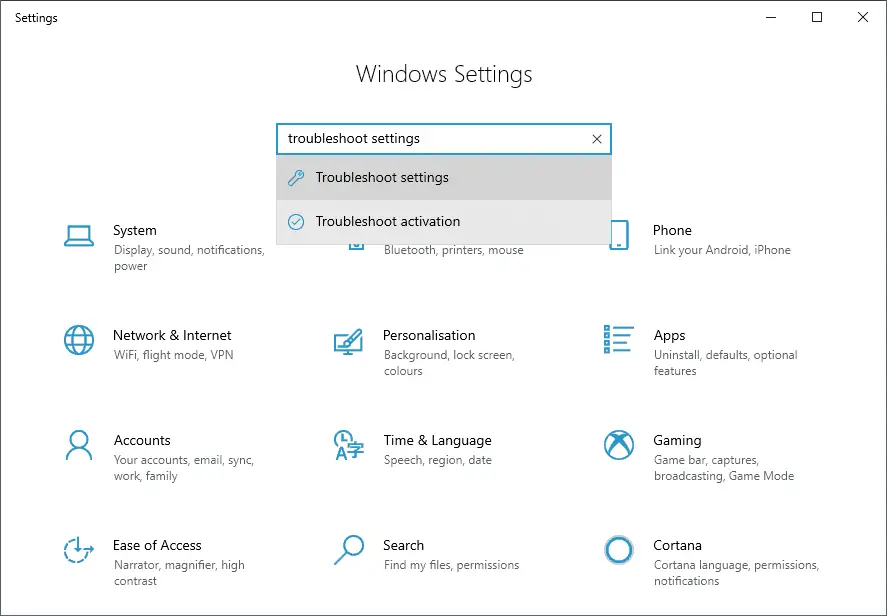
- Press Windows Key + I keyboard shortcut. This will open Windows settings.
- Now search for “Troubleshoot Settings” and click Troubleshoot settings from the result.
- Under Troubleshoot, locate and open Internet Connections. Click on it and press Run the trobleshooter.
- Click on Troubleshoot my connections to the internet.
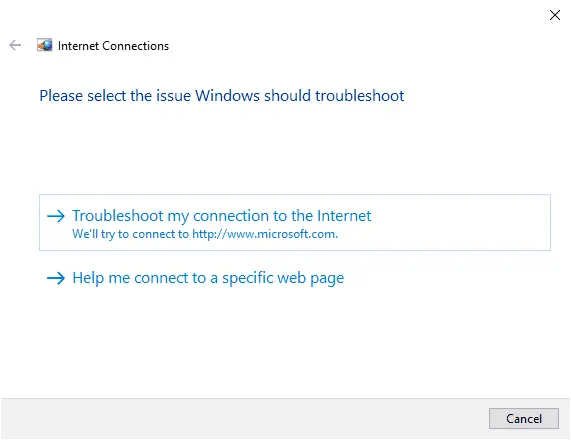
- Let the troubleshooter complete the tests and will report you back with problems it found and fixes that were applied.
- That’s it. Check your internet connection to confirm DNS server not responding issue is fixed or not.
7. Check your Router/Modem
If you are using router or modem to connect to internet, then try restarting your router or modem. Also make sure to switch the ethernet port and use different port available on your router. If you had recently changed any settings if your wifi router that it could be leading cause of DNS server not responding error.
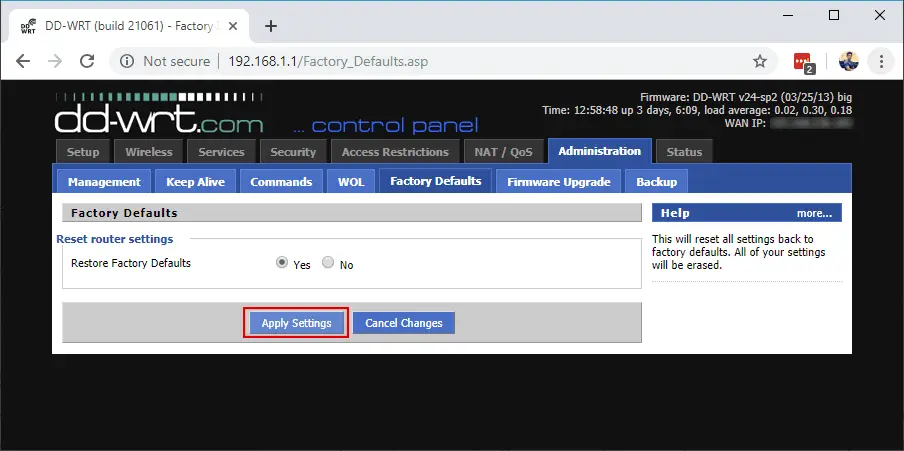
Reverting wifi router to old settings or resetting to factory default may fix your problem. Do keep in mind, you will lose all the internet settings related to your ISP if you perform factory reset. It would be best to contact your internet service provider and let them have look at your Internet connection.

